HOWTO setup OpenVPN server and client configuration files using EasyRSA
Introduction
OpenVPN allows client computers to tunnel into a server over a single UDP or TCP port securely. This HOWTO article is a step-by-step guide that explains how to create the server and client OpenVPN configuration files that makes this possible. In the process this article explains how to create the public key infrastructure (PKI) so that a client can securely communicate with the server. OpenSSL is the foundation for the security functionality of OpenVPN.For this tutorial you will need the following software:
- OpenVPN. You can download the latest version of OpenVPN from https://openvpn.net/index.php/open-source/downloads.html
- EasyRSA is the tool people use to create the Public Key Infrastructure (PKI) for OpenVPN. Download the latest release of EasyRSA from https://github.com/OpenVPN/easy-rsa/releases. There is not installation required. Extract the contents of the archive into a folder.
Assumptions
The tutorial assumes that:- You installed OpenVPN on your computer accepting all defaults.
- The public IP address of your server is aaa.bbb.ccc.ddd. You can find your public (internet-facing) IP address by Googling “What is my IP Address”.
- The protocol and port OpenVPN will communicate on. This tutorial will assume port UDP 1175. You need to ensure that this port is forwarded to your computer if you are behind a router and any Firewall entries are opened up.
Procedure
Preparation
Extract the EasyRSA archive into two folders. I called one EasyRSA-server and the other EasyRSA-client1. For the purpose of this tutorial the folders the folders are on the same computer.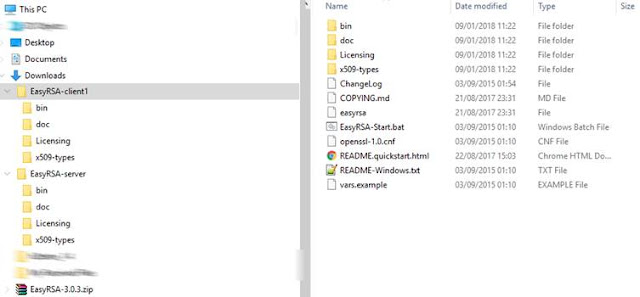
On The Client
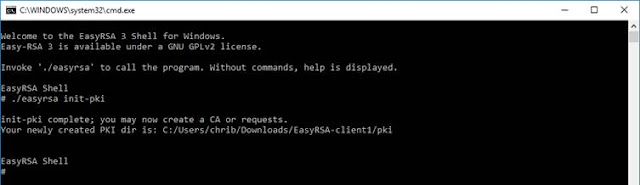
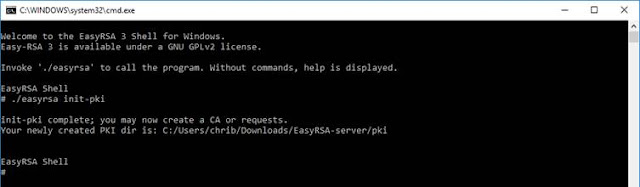
From within Windows File explorer go to the EasyRSA-client1 directory and double click on EasyRSA-start.bat. This will open the EasyRSA 3 Shell for Windows.Initialise the environment and setup the folder structure for the client PKI.
./easyrsa init-pki
The command below will generate the client’s private key and it’s Certificate Signing Request (CSR). The client in this tutorial is called Client1.
./easyrsa gen-req Client1 nopass
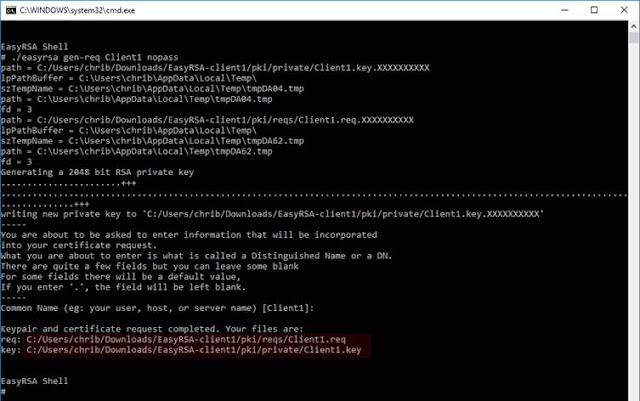
The location of private key and CSR are displayed in the command window. The private key will used in the client’s config file while the CSR will be signed by the server.
On the server
From Windows File explorer open the EasyRSA-server directory and double click on EasyRSA-start.bat.Type the command to generate the pre-shared key (PSK). This key is used by both the server and the clients to sign packets using this PSK. It constitutes an added layer of protection to the TLS channel.
openvpn --genkey --secret ta.key
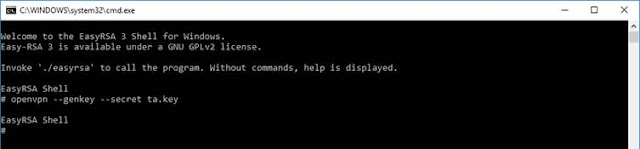
This command creates the file ./ta.key. The contents of this file will be embedded in both the server and client configuration files.
Initialise the environment and setup the folder structure for the PKI:
./easyrsa init-pki
Generate the Diffie–Hellman key. This key makes it possible to exchange cryptographic keys between the server and clients securely.
./easyrsa gen-dh
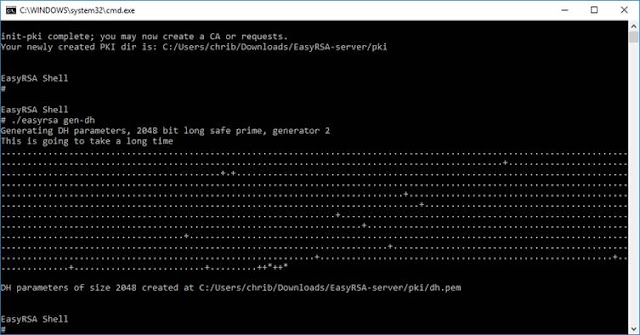
The generated file \pki\dh.pem will be referenced in the server config file.
The Certificate Authority (CA) framework is generated by the command below. In this article the server will assume the role of issuing digital certificates.
./easyrsa build-ca nopass
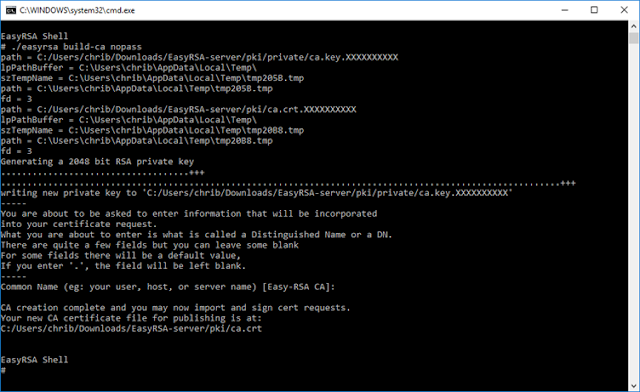
For the Common Name I kept the default.
The generated file \pki\ca.crt will be used in the server config file.
The private and public keys of the server are generated by the command below:
./easyrsa build-server-full OVPN-SERVER nopass
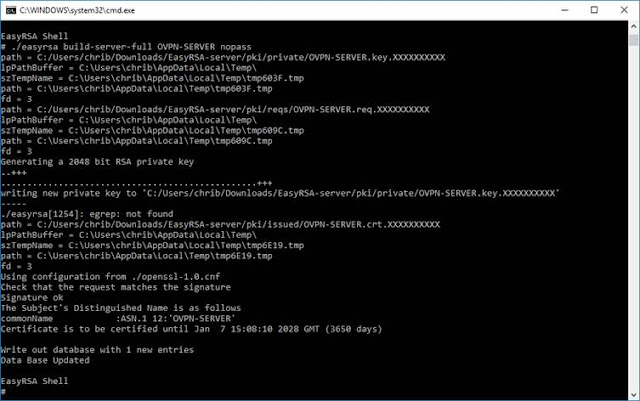
OVPN-SERVER represents the name of the server.
The files \pki\issued\OVPN-SERVER.crt and \pki\private\OVPN-SERVER.key will be generated. They will be used in the server config file.
On the server: Processing the client CSR
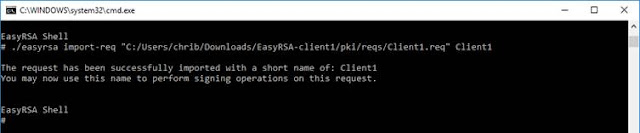
The command below imports the client’s CSR.
./easyrsa import-req “C:/Users/chrib/Downloads/EasyRSA-client/pki/reqs/Client1.req” Client1
Once imported, the CSR needs to be signed by the server. You need to confirm that you want to sign the client certificate by typing in yes.
./easyrsa sign-req client Client1 nopass
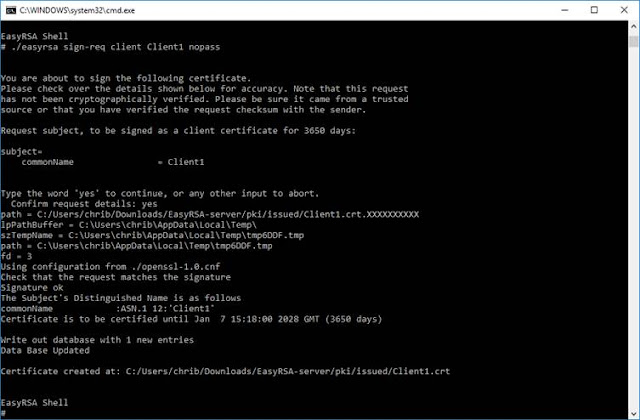
A file called \pki\issued\Client1.crt> will be generated on the server. Part of this file will be incorporated into the client config.
The client and server EasyRSA windows may be closed by typing Exit in them
Assembling the server configuration file.
The server configuration file will be based upon a file called server.ovpn that is located at C:\Program Files\OpenVPN\sample-config. Copy it from this location to C:\Program Files\OpenVPN\config and open the file in a text editor.- Transfer the file dh.pem from the EasyRSA-server\pki folder to the C:\Program Files\OpenVPN\config folder.
- In server.ovpn modify the section Diffie hellman parameters and modify the entry dh with a reference to the file you pasted in step (1).
dh dh.pem - OpenVPN allows the Certificate authority (ca), Server Certificate (cert) and Server Private Key (key) to be either linked to from the config file or be embedded within the same. In this example I am embedding them. Therefore the lines that point to these files need to be commented out by preceding them with the semicolon symbol (;):
;ca "C:\\Program Files\\OpenVPN\\config\\ca.crt"
;cert "C:\\Program Files\\OpenVPN\\config\\server.crt"
;key "C:\\Program Files\\OpenVPN\\config\\server.key" - Change the port OpenVPN server will be listening on. In this tutorial it is 1175:
port 1175 - Check that the protocol you want to use is the one that is enabled. Delete or comment out the one that is not applicable For this tutorial this is UDP:
;proto tcp
proto udp - At the end of the file paste the Certificate Authority code. You can find it in the EasyRSA-server\pki\ca.crt file. Simply copy the text from this file and place it at the end of the server.ovpn file within <ca> … </ca> tags.
- At the end of the file paste the Signed Server Certificate. You can find it in the EasyRSA-server\pki\issued\OVPN-SERVER.crt file. Simply copy the text from “-----BEGIN CERTIFICATE-----“ to “-----END CERTIFICATE-----“ from this file and place it at the end of the server.ovpn file within <cert> … </cert> tags. Other generated text does not need to be transferred.
- At the end of the file paste the Server’s Private Key. You can find it in the EasyRSA-server\pki\private\OVPN-SERVER.key file. Simply copy the text from “-----BEGIN PRIVATE KEY-----“ to “-----END PRIVATE KEY----- “ from this file and place it at the end of the server.ovpn file within <key> … </key> tags. Please note that this represents the private key of the server and should be protected.
- As the TLS key will be embedded within the server config file rather than be an external file the line that references it needs to be replaced as follows:
;tls-auth ta.key 0 # This file is secret
key-direction 0 # This file is secret. - Open EasyRSA-server\ta.key file and copy the text from “-----BEGIN OpenVPN Static key V1----- “ to “-----END OpenVPN Static key V1----- “ from this file and place it at the end of the server.ovpn file within <tls-auth> … </tls-auth> tags.
- Save the file and restart the OpenVPN service. Check the log file at C:\Program Files\OpenVPN\log\server.log. A sample of this log file is given below. If you get an error you need to sort it out before continuing.
Assembling the client configuration file.
The client configuration file will be based upon the sample client.ovpn found in C:\Program Files\OpenVPN\sample-config. Copy it to a location from where you will later on import it into the client. In this tutorial the config file will be called client1.ovpn.- Modify the section that indicates the server and the port it is listening on to reflect your server:
;remote my-server-1 1194
remote aaa.bbb.ccc.ddd 1175 - Check that the protocol you want to use is the one that is enabled. Delete or comment out the one that is not applicable For this tutorial this is UDP:
;proto tcp
proto udp - As with the server, the various certificates will be embedded within the configuration file itself rather than be external files. The certificate authority, client certificate and client private key references will be commented out by preceeding them with a semi-colon:
;ca ca.crt
;cert client.crt
;key client.key - The certificate authority is the same as the server. Simply copy this section from the server configuration file (or from EasyRSA-server\pki\ca.crt file).
- At the end of the file paste the Client Certificate. You can find it in the EasyRSA-server\pki\issued\Client1.crt file. Simply copy the text from “-----BEGIN CERTIFICATE-----“ to “-----END CERTIFICATE-----“ from this file and place it at the end of the client1.ovpn file within <cert> … </cert> tags. Other generated text does not need to be transferred.
- At the end of the file paste the Client private key. You can find it in the EasyRSA-client1\pki\private\Client1.key file. Simply copy the text from “-----BEGIN PRIVATE KEY-----“ to “-----END PRIVATE KEY-----“ from this file and place it at the end of the client1.ovpn file within <key> … </key> tags.
- As the TLS key will be embedded within the client config file rather than be an external file the line that references it needs to be replaced as follows:
;tls-auth ta.key 1
key-direction 1 - Copy the section <tls-auth> … </tls-auth> from the server configuration file or copy the contents from the source file EasyRSA-server\ta.key.
- Save the file and import it into the OpenVPN client.
Server Configuration File (server.ovpn)
#################################################
# Sample OpenVPN 2.0 config file for #
# multi-client server. #
# #
# This file is for the server side #
# of a many-clients <-> one-server #
# OpenVPN configuration. #
# #
# OpenVPN also supports #
# single-machine <-> single-machine #
# configurations (See the Examples page #
# on the web site for more info). #
# #
# This config should work on Windows #
# or Linux/BSD systems. Remember on #
# Windows to quote pathnames and use #
# double backslashes, e.g.: #
# "C:\\Program Files\\OpenVPN\\config\\foo.key" #
# #
# Comments are preceded with '#' or ';' #
#################################################
# Which local IP address should OpenVPN
# listen on? (optional)
;local a.b.c.d
# Which TCP/UDP port should OpenVPN listen on?
# If you want to run multiple OpenVPN instances
# on the same machine, use a different port
# number for each one. You will need to
# open up this port on your firewall.
#port 1194
port 1175
# TCP or UDP server?
;proto tcp
proto udp
# "dev tun" will create a routed IP tunnel,
# "dev tap" will create an ethernet tunnel.
# Use "dev tap0" if you are ethernet bridging
# and have precreated a tap0 virtual interface
# and bridged it with your ethernet interface.
# If you want to control access policies
# over the VPN, you must create firewall
# rules for the the TUN/TAP interface.
# On non-Windows systems, you can give
# an explicit unit number, such as tun0.
# On Windows, use "dev-node" for this.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel if you
# have more than one. On XP SP2 or higher,
# you may need to selectively disable the
# Windows firewall for the TAP adapter.
# Non-Windows systems usually don't need this.
;dev-node MyTap
# SSL/TLS root certificate (ca), certificate
# (cert), and private key (key). Each client
# and the server must have their own cert and
# key file. The server and all clients will
# use the same ca file.
#
# See the "easy-rsa" directory for a series
# of scripts for generating RSA certificates
# and private keys. Remember to use
# a unique Common Name for the server
# and each of the client certificates.
#
# Any X509 key management system can be used.
# OpenVPN can also use a PKCS #12 formatted key file
# (see "pkcs12" directive in man page).
;ca ca.crt
;cert server.crt
;key server.key # This file should be kept secret
# Diffie hellman parameters.
# Generate your own with:
# openssl dhparam -out dh2048.pem 2048
dh dh.pem
# Network topology
# Should be subnet (addressing via IP)
# unless Windows clients v2.0.9 and lower have to
# be supported (then net30, i.e. a /30 per client)
# Defaults to net30 (not recommended)
;topology subnet
# Configure server mode and supply a VPN subnet
# for OpenVPN to draw client addresses from.
# The server will take 10.8.0.1 for itself,
# the rest will be made available to clients.
# Each client will be able to reach the server
# on 10.8.0.1. Comment this line out if you are
# ethernet bridging. See the man page for more info.
server 10.8.0.0 255.255.255.0
# Maintain a record of client <-> virtual IP address
# associations in this file. If OpenVPN goes down or
# is restarted, reconnecting clients can be assigned
# the same virtual IP address from the pool that was
# previously assigned.
ifconfig-pool-persist ipp.txt
# Configure server mode for ethernet bridging.
# You must first use your OS's bridging capability
# to bridge the TAP interface with the ethernet
# NIC interface. Then you must manually set the
# IP/netmask on the bridge interface, here we
# assume 10.8.0.4/255.255.255.0. Finally we
# must set aside an IP range in this subnet
# (start=10.8.0.50 end=10.8.0.100) to allocate
# to connecting clients. Leave this line commented
# out unless you are ethernet bridging.
;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100
# Configure server mode for ethernet bridging
# using a DHCP-proxy, where clients talk
# to the OpenVPN server-side DHCP server
# to receive their IP address allocation
# and DNS server addresses. You must first use
# your OS's bridging capability to bridge the TAP
# interface with the ethernet NIC interface.
# Note: this mode only works on clients (such as
# Windows), where the client-side TAP adapter is
# bound to a DHCP client.
;server-bridge
# Push routes to the client to allow it
# to reach other private subnets behind
# the server. Remember that these
# private subnets will also need
# to know to route the OpenVPN client
# address pool (10.8.0.0/255.255.255.0)
# back to the OpenVPN server.
;push "route 192.168.10.0 255.255.255.0"
;push "route 192.168.20.0 255.255.255.0"
# To assign specific IP addresses to specific
# clients or if a connecting client has a private
# subnet behind it that should also have VPN access,
# use the subdirectory "ccd" for client-specific
# configuration files (see man page for more info).
# EXAMPLE: Suppose the client
# having the certificate common name "Thelonious"
# also has a small subnet behind his connecting
# machine, such as 192.168.40.128/255.255.255.248.
# First, uncomment out these lines:
;client-config-dir ccd
;route 192.168.40.128 255.255.255.248
# Then create a file ccd/Thelonious with this line:
# iroute 192.168.40.128 255.255.255.248
# This will allow Thelonious' private subnet to
# access the VPN. This example will only work
# if you are routing, not bridging, i.e. you are
# using "dev tun" and "server" directives.
# EXAMPLE: Suppose you want to give
# Thelonious a fixed VPN IP address of 10.9.0.1.
# First uncomment out these lines:
;client-config-dir ccd
;route 10.9.0.0 255.255.255.252
# Then add this line to ccd/Thelonious:
# ifconfig-push 10.9.0.1 10.9.0.2
# Suppose that you want to enable different
# firewall access policies for different groups
# of clients. There are two methods:
# (1) Run multiple OpenVPN daemons, one for each
# group, and firewall the TUN/TAP interface
# for each group/daemon appropriately.
# (2) (Advanced) Create a script to dynamically
# modify the firewall in response to access
# from different clients. See man
# page for more info on learn-address script.
;learn-address ./script
# If enabled, this directive will configure
# all clients to redirect their default
# network gateway through the VPN, causing
# all IP traffic such as web browsing and
# and DNS lookups to go through the VPN
# (The OpenVPN server machine may need to NAT
# or bridge the TUN/TAP interface to the internet
# in order for this to work properly).
;push "redirect-gateway def1 bypass-dhcp"
# Certain Windows-specific network settings
# can be pushed to clients, such as DNS
# or WINS server addresses. CAVEAT:
# http://openvpn.net/faq.html#dhcpcaveats
# The addresses below refer to the public
# DNS servers provided by opendns.com.
;push "dhcp-option DNS 208.67.222.222"
;push "dhcp-option DNS 208.67.220.220"
# Uncomment this directive to allow different
# clients to be able to "see" each other.
# By default, clients will only see the server.
# To force clients to only see the server, you
# will also need to appropriately firewall the
# server's TUN/TAP interface.
;client-to-client
# Uncomment this directive if multiple clients
# might connect with the same certificate/key
# files or common names. This is recommended
# only for testing purposes. For production use,
# each client should have its own certificate/key
# pair.
#
# IF YOU HAVE NOT GENERATED INDIVIDUAL
# CERTIFICATE/KEY PAIRS FOR EACH CLIENT,
# EACH HAVING ITS OWN UNIQUE "COMMON NAME",
# UNCOMMENT THIS LINE OUT.
;duplicate-cn
# The keepalive directive causes ping-like
# messages to be sent back and forth over
# the link so that each side knows when
# the other side has gone down.
# Ping every 10 seconds, assume that remote
# peer is down if no ping received during
# a 120 second time period.
keepalive 10 120
# For extra security beyond that provided
# by SSL/TLS, create an "HMAC firewall"
# to help block DoS attacks and UDP port flooding.
#
# Generate with:
# openvpn --genkey --secret ta.key
#
# The server and each client must have
# a copy of this key.
# The second parameter should be '0'
# on the server and '1' on the clients.
;tls-auth ta.key 0 # This file is secret
key-direction 0
# Select a cryptographic cipher.
# This config item must be copied to
# the client config file as well.
# Note that v2.4 client/server will automatically
# negotiate AES-256-GCM in TLS mode.
# See also the ncp-cipher option in the manpage
cipher AES-256-CBC
# Enable compression on the VPN link and push the
# option to the client (v2.4+ only, for earlier
# versions see below)
;compress lz4-v2
;push "compress lz4-v2"
# For compression compatible with older clients use comp-lzo
# If you enable it here, you must also
# enable it in the client config file.
;comp-lzo
# The maximum number of concurrently connected
# clients we want to allow.
;max-clients 100
# It's a good idea to reduce the OpenVPN
# daemon's privileges after initialization.
#
# You can uncomment this out on
# non-Windows systems.
;user nobody
;group nobody
# The persist options will try to avoid
# accessing certain resources on restart
# that may no longer be accessible because
# of the privilege downgrade.
persist-key
persist-tun
# Output a short status file showing
# current connections, truncated
# and rewritten every minute.
status openvpn-status.log
# By default, log messages will go to the syslog (or
# on Windows, if running as a service, they will go to
# the "\Program Files\OpenVPN\log" directory).
# Use log or log-append to override this default.
# "log" will truncate the log file on OpenVPN startup,
# while "log-append" will append to it. Use one
# or the other (but not both).
;log openvpn.log
;log-append openvpn.log
# Set the appropriate level of log
# file verbosity.
#
# 0 is silent, except for fatal errors
# 4 is reasonable for general usage
# 5 and 6 can help to debug connection problems
# 9 is extremely verbose
verb 3
# Silence repeating messages. At most 20
# sequential messages of the same message
# category will be output to the log.
;mute 20
# Notify the client that when the server restarts so it
# can automatically reconnect.
explicit-exit-notify 1
<ca>
-----BEGIN CERTIFICATE-----
MIIDNTCCAh2gAwIBAgIJAK55XeHWQZ7mMA0GCSqGSIb3DQEBCwUAMBYxFDASBgNV
BAMMC0Vhc3ktUlNBIENBMB4XDTE4MDExOTEzMzgwNVoXDTI4MDExNzEzMzgwNVow
<< cropped >>
1dJk/vQHQE5sXoFKawskjhgpc9yHWOCSOtIU86daBXeECCVDwvvDC4ZsxTS+kezm
EjKjt6DbTglu
-----END CERTIFICATE-----
</ca>
<cert>
-----BEGIN CERTIFICATE-----
MIIDZzCCAk+gAwIBAgIRAMQ9M94i6yLYdxJU3ptEWjAwDQYJKoZIhvcNAQELBQAw
FjEUMBIGA1UEAwwLRWFzeS1SU0EgQ0EwHhcNMTgwMTE5MTM0MDE2WhcNMjgwMTE3
<< cropped >>
oYb4/rWR2Mdc0QtDbBOYsDPg35ALzamsz/I0/RGZYESfZb3Rq+Bt+5qSZFSejEWF
yEnC0+pnDL74xBs=
-----END CERTIFICATE-----
</cert>
<key>
-----BEGIN PRIVATE KEY-----
MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDfjxqCF58DB2fu
+v1zWmvxXrlq3/sT6vCj0dIoqHg6Tuhz9HEm9pLF5wEAa9tujBJDQoSDkrAY1ajJ
<< cropped >>
n1y4GEaKohfBqdC5tA+SOHFEAvLIMBDT4EVHRJc5chE9lvJVAtgZCV+da7ZXQNMf
I6kseuB0B1eorJ+M69KGJ2lH
-----END PRIVATE KEY-----
</key>
<tls-auth>
-----BEGIN OpenVPN Static key V1-----
ab02f38877b948fa44ecb789a0090279
7f9d17b84ee4024cbd7521569a130aec
<< cropped >>
fadbf862c59b22796efe6074b2a8ad28
5086c909f72fce1f3a27ee4ebc39bdb4
-----END OpenVPN Static key V1-----
</tls-auth>
Client Configuration File (client1.ovpn)
##############################################
# Sample client-side OpenVPN 2.0 config file #
# for connecting to multi-client server. #
# #
# This configuration can be used by multiple #
# clients, however each client should have #
# its own cert and key files. #
# #
# On Windows, you might want to rename this #
# file so it has a .ovpn extension #
##############################################
# Specify that we are a client and that we
# will be pulling certain config file directives
# from the server.
client
# Use the same setting as you are using on
# the server.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel
# if you have more than one. On XP SP2,
# you may need to disable the firewall
# for the TAP adapter.
;dev-node MyTap
# Are we connecting to a TCP or
# UDP server? Use the same setting as
# on the server.
;proto tcp
proto udp
# The hostname/IP and port of the server.
# You can have multiple remote entries
# to load balance between the servers.
remote aaa.bbb.ccc.ddd 1175
# Choose a random host from the remote
# list for load-balancing. Otherwise
# try hosts in the order specified.
;remote-random
# Keep trying indefinitely to resolve the
# host name of the OpenVPN server. Very useful
# on machines which are not permanently connected
# to the internet such as laptops.
resolv-retry infinite
# Most clients don't need to bind to
# a specific local port number.
nobind
# Downgrade privileges after initialization (non-Windows only)
;user nobody
;group nobody
# Try to preserve some state across restarts.
persist-key
persist-tun
# If you are connecting through an
# HTTP proxy to reach the actual OpenVPN
# server, put the proxy server/IP and
# port number here. See the man page
# if your proxy server requires
# authentication.
;http-proxy-retry # retry on connection failures
;http-proxy [proxy server] [proxy port #]
# Wireless networks often produce a lot
# of duplicate packets. Set this flag
# to silence duplicate packet warnings.
;mute-replay-warnings
# SSL/TLS parms.
# See the server config file for more
# description. It's best to use
# a separate .crt/.key file pair
# for each client. A single ca
# file can be used for all clients.
;ca ca.crt
;cert client.crt
;key client.key
# Verify server certificate by checking that the
# certicate has the correct key usage set.
# This is an important precaution to protect against
# a potential attack discussed here:
# http://openvpn.net/howto.html#mitm
#
# To use this feature, you will need to generate
# your server certificates with the keyUsage set to
# digitalSignature, keyEncipherment
# and the extendedKeyUsage to
# serverAuth
# EasyRSA can do this for you.
remote-cert-tls server
# If a tls-auth key is used on the server
# then every client must also have the key.
#tls-auth ta.key 1
key-direction 1
# Select a cryptographic cipher.
# If the cipher option is used on the server
# then you must also specify it here.
# Note that v2.4 client/server will automatically
# negotiate AES-256-GCM in TLS mode.
# See also the ncp-cipher option in the manpage
cipher AES-256-CBC
# Enable compression on the VPN link.
# Don't enable this unless it is also
# enabled in the server config file.
#comp-lzo
# Set log file verbosity.
verb 3
# Silence repeating messages
;mute 20
<ca>
-----BEGIN CERTIFICATE-----
MIIDNTCCAh2gAwIBAgIJAK55XeHWQZ7mMA0GCSqGSIb3DQEBCwUAMBYxFDASBgNV
BAMMC0Vhc3ktUlNBIENBMB4XDTE4MDExOTEzMzgwNVoXDTI4MDExNzEzMzgwNVow
<< cropped >>
1dJk/vQHQE5sXoFKawskjhgpc9yHWOCSOtIU86daBXeECCVDwvvDC4ZsxTS+kezm
EjKjt6DbTglu
-----END CERTIFICATE-----
</ca>
<cert>
-----BEGIN CERTIFICATE-----
MIIDSjCCAjKgAwIBAgIQH6opQqoq+FAE+Tc5pDNNGDANBgkqhkiG9w0BAQsFADAW
MRQwEgYDVQQDDAtFYXN5LVJTQSBDQTAeFw0xODAxMTkxMzQ1MzdaFw0yODAxMTcx
<< cropped >>
wmHCrmpz+amvJ1tbSsdiNwPhgnpYOrg0sID1E47x4qMqtuGPBdsPiSAxjEYD3J0q
oIX27YjOK/zpiq3LLjKShOejZVG7tCP7MeSBi3Tl
-----END CERTIFICATE-----
</cert>
<key>
-----BEGIN PRIVATE KEY-----
MIIEvQIBADANBgkqhkiG9w0BAQEFAASCBKcwggSjAgEAAoIBAQDKY3ArtEvOQRwY
DK+1m1x3k+K3SbBgNV6wkAxjiYoznnR4pRdPA5YtZiw18HjpWf0Yqf5r8LGro+tP
<< cropped >>
52eSKvqtVCI+rd4xmsY7PzJgwRmmYIV0kbZr6TqfR4VzQcbovE0vhL78BC1HTTtt
o0Lvw0S4fAx9ttl2vgt2r4A=
-----END PRIVATE KEY-----
</key>
<tls-auth>
-----BEGIN OpenVPN Static key V1-----
ab02f38877b948fa44ecb789a0090279
7f9d17b84ee4024cbd7521569a130aec
<< cropped >>
fadbf862c59b22796efe6074b2a8ad28
5086c909f72fce1f3a27ee4ebc39bdb4
-----END OpenVPN Static key V1-----
</tls-auth>
Server.log file
Fri Jan 19 17:02:36 2018 OpenVPN 2.4.4 x86_64-w64-mingw32 [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Sep 26 201
Fri Jan 19 17:02:36 2018 Windows version 6.2 (Windows 8 or greater) 64bit
Fri Jan 19 17:02:36 2018 library versions: OpenSSL 1.0.2l 25 May 2017, LZO 2.10
Fri Jan 19 17:02:36 2018 NOTE: your local LAN uses the extremely common subnet address 192.168.0.x or 192.168.1.x. Be aware that this might create routing conflicts if you connect to the VPN server from public locations such as internet cafes that use the same subnet.
Fri Jan 19 17:02:36 2018 Diffie-Hellman initialized with 2048 bit key
Fri Jan 19 17:02:36 2018 Outgoing Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Fri Jan 19 17:02:36 2018 Incoming Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Fri Jan 19 17:02:36 2018 interactive service msg_channel=0
Fri Jan 19 17:02:36 2018 ROUTE_GATEWAY 192.168.1.1/255.255.255.0 I=3 HWADDR=xx:xx:xx:xx:xx:xx
Fri Jan 19 17:02:36 2018 open_tun
Fri Jan 19 17:02:36 2018 TAP-WIN32 device [Ethernet 2] opened: \\.\Global\{A9A68054-AEB8-4F5F-AFF9-768704AD1DFB}.tap
Fri Jan 19 17:02:36 2018 TAP-Windows Driver Version 9.21
Fri Jan 19 17:02:36 2018 Notified TAP-Windows driver to set a DHCP IP/netmask of 10.8.0.1/255.255.255.252 on interface {A9A68054-AEB8-4F5F-AFF9-768704AD1DFB} [DHCP-serv: 10.8.0.2, lease-time: 31536000]
Fri Jan 19 17:02:36 2018 Sleeping for 10 seconds...
Fri Jan 19 17:02:46 2018 Successful ARP Flush on interface [6] {A9A68054-AEB8-4F5F-AFF9-768704AD1DFB}
Fri Jan 19 17:02:46 2018 do_ifconfig, tt->did_ifconfig_ipv6_setup=0
Fri Jan 19 17:02:46 2018 C:\WINDOWS\system32\route.exe ADD 10.8.0.0 MASK 255.255.255.0 10.8.0.2
Fri Jan 19 17:02:46 2018 ROUTE: CreateIpForwardEntry succeeded with dwForwardMetric1=35 and dwForwardType=4
Fri Jan 19 17:02:46 2018 Route addition via IPAPI succeeded [adaptive]
Fri Jan 19 17:02:46 2018 Could not determine IPv4/IPv6 protocol. Using AF_INET6
Fri Jan 19 17:02:46 2018 Socket Buffers: R=[65536->65536] S=[65536->65536]
Fri Jan 19 17:02:46 2018 setsockopt(IPV6_V6ONLY=0)
Fri Jan 19 17:02:46 2018 UDPv6 link local (bound): [AF_INET6][undef]:1194
Fri Jan 19 17:02:46 2018 UDPv6 link remote: [AF_UNSPEC]
Fri Jan 19 17:02:46 2018 MULTI: multi_init called, r=256 v=256
Fri Jan 19 17:02:46 2018 IFCONFIG POOL: base=10.8.0.4 size=62, ipv6=0
Fri Jan 19 17:02:46 2018 IFCONFIG POOL LIST
Fri Jan 19 17:02:46 2018 Initialization Sequence Completed
Thank you for this tutorial!
ReplyDeleteI've been trying to get this workin for a while now and this got me on the right track.
Other things I had to do:
I copied the easy-rsa-cleint and easy-rsa-server folders to a c:\FolderName to get past some windows 10 permission issues.
On the server "openvpn --genkey --secret ta.key " gave me an error "can not find bin/sh openvpn" I changed teh command to directly reference the location as follows: ['C:/Program Files/OpenVPN/bin/'openvpn --genkey --secret ta.key ] note the ' in the path to get the space to work in the path name.
Hello,
DeleteThank for the update. This tutorial is based on a Windows platform. Where you using a Windows platform?
How to generate client certificate for more than 2 year period(default)?
ReplyDeleteYou need to edit a number of files within easy-rsa. Search within the bat files and replace the parameter '-days 3650' with a larger value. 10 years would be approx 36500
Delete10 years is 3650 days
DeleteI generated Client1.req on client side. (./easyrsa gen-req Client1 nopass) But when i proceed "./easyrsa import-req “C:/Users/chrib/Downloads/EasyRSA-client/pki/reqs/Client1.req” Client1 " on server side. It warms me which is not valid certificate. ( I change the path with my user name). What can be the reason of it ?
ReplyDeleteSorry. Top of my head I can't see why the certificate should not be invalid. Are you sure you are referencing the right cert?
ReplyDelete